In March 2025, Lovable — a popular AI-driven app builder — had a security hole that accidentally exposed user data. Apps built on the platform shipped with access controls that didn't actually control access. The story is worth re-reading not because Lovable is uniquely bad — they responded responsibly and patched fast — but because the failure mode is the default for every vibe-coding platform on the market right now.
What actually happened
Without going deep into the technical details: the platform generated apps where the database access layer trusted the client to enforce permissions. In other words, the bouncer at the club was a sticker that said “please don't come in if you weren't invited.”
Anyone who knew how to send the right database query directly — bypassing the app's UI — could read data they had no right to see. That's a textbook authorisation bug. It's the first thing every backend security review looks for. Yet AI-generated code missed it consistently because nobody asked the AI to add the check that wasn't obvious from the prompt.
Three things broke:
- 🔓 The bouncer let everyone in. Authorisation checks weren't enforced server-side.
- 🤖 Over-trusting AI-generated code. The platform shipped what the model produced without a security review.
- 📱 Affected every app on the platform. Not a one-off bug — a class of bug that inherited.
Why this matters beyond Lovable
Vibe coding — describing what you want in English and letting an AI generate the implementation — is the single fastest-growing way to build software in 2026. It's wonderful for prototypes, glue code, and internal tools. It's genuinely transformative for non-engineers who can now ship working apps in a weekend.
It's also a textbook trap. The AI is incredibly good at producing code that looks right andworks on the happy path. The same model is mediocre at producing code that's defensible against adversaries — because adversarial scenarios aren't in the natural-language description of the feature.
If you described a checkout flow, the AI built a checkout flow. It didn't add idempotency keys. It didn't reject negative quantities. It didn't check that the user paying for the order is the user who placed it. None of those things were in the prompt. None of them are visible from the UI. All of them are real attacks happening every day.
Multiply this across thousands of vibe-coded apps now in production, and you have the next decade's application-security workload right there.
Three simple protections that catch this class of bug
Double-check the AI's work
Would you trust a robot to lock your front door without checking? Don't trust it to lock your database either. For any AI-generated code touching data or auth, a human with security training has to read it before it ships. Not a code review by another AI. A human who knows what authorisation bypass looks like.
In practice this means: a security checklist (server-side auth checks, input validation, rate limiting, idempotency, error handling) that gets ticked off before the app goes live. The checklist is boring; the absence of one is the bug.
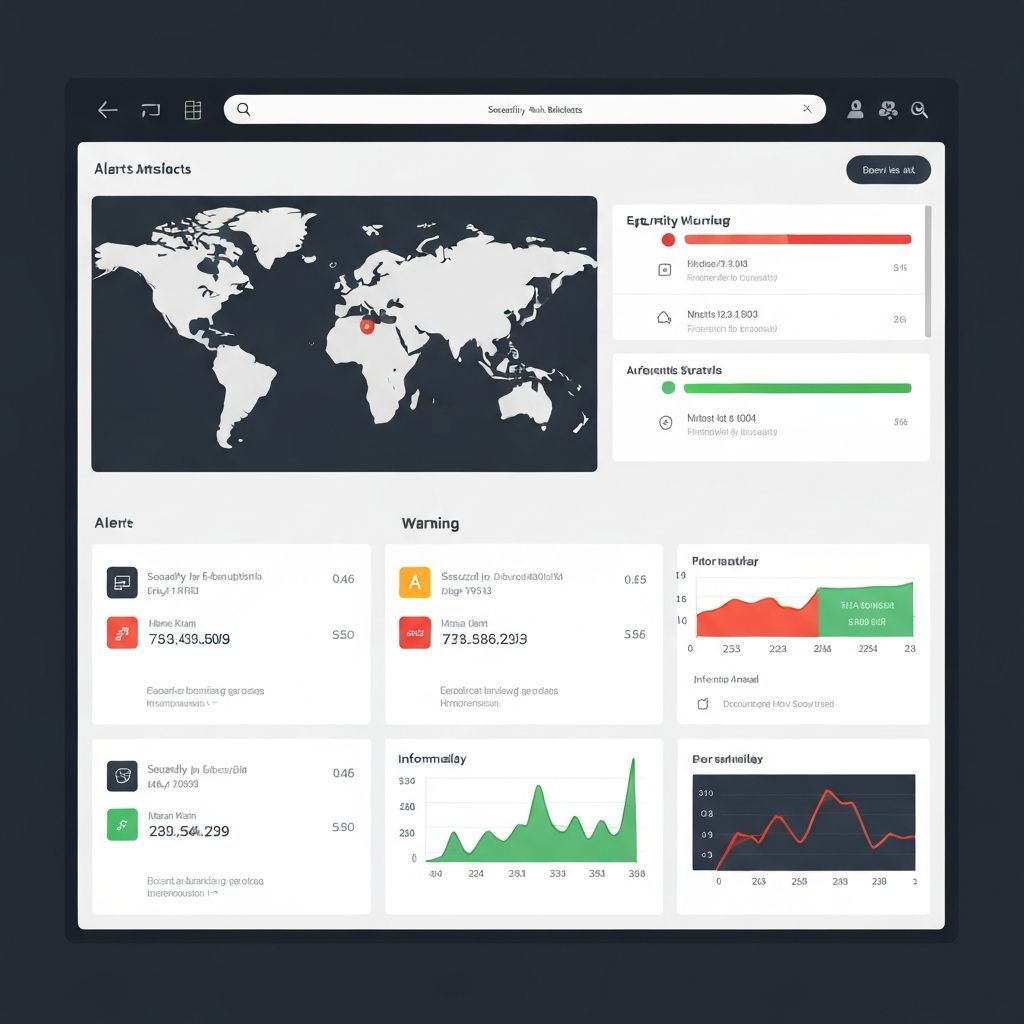
Assume mistakes happen — monitor for them
You're going to miss something. Plan for it. Production monitoring needs to detect odd activity: spikes in failed auth attempts, requests for resources the user shouldn't have, queries to endpoints the UI doesn't expose. The first time you see one of these, it's either a bug or an attack. Either way you want to know within minutes, not weeks.
Build the alerting before you launch. Once the breach has happened, you've missed your window to catch it cheaply.
Limit access — to data and to capabilities
Only give employees and processes exactly what they need. The principle of least privilege isn't glamorous, but it's the difference between a bug becoming an annoyance and a bug becoming a breach.
For AI-built apps specifically: the database role the app uses should only see the columns the app actually displays. The API key the app uses should only call the endpoints it actually invokes. The deployed environment should only have the secrets it actually needs. Every dimension of access is a dimension the attacker can't exceed.
A practical checklist before you ship an AI-built app
If you're shipping a vibe-coded app, walk through this list. It's short on purpose:
- Server-side authorisation on every endpoint. Never trust the client. If the API can return another user's data when called directly, you have a bug.
- Input validation at the boundary. Type, range, length, format. Reject bad input loudly rather than silently coercing it.
- Rate limiting on auth endpoints. Login, password reset, sign-up. Otherwise credential stuffing is free.
- Secrets out of the code. Environment variables, secret manager, never committed to git.
- Database role with minimum privileges. The app's DB user shouldn't be able to drop tables.
- Logging on every sensitive action. Reads, writes, deletes, auth events. Stored somewhere you can query them.
- An incident response plan. If a breach happens at 3am, who gets paged, and what do they do in the first 60 minutes?
None of these are AI-specific. They're application-security basics. The reason to call them out for vibe-coded apps is that AI-generated code skips them by default — and the people deploying the code often don't know what to look for.
AI is the new junior employee
The framing that helps me most: AI is like a brilliant new junior employee. Amazing potential. Will work 24/7. Has read every textbook on the subject. But also: needs supervision, doesn't know what it doesn't know, and will confidently do the wrong thing if you don't check.
You wouldn't hand a junior engineer the production database keys on day one. Don't hand them to an AI either.
What to do next
If you're running AI-built apps at any scale, two routes:
- Need to find every AI-built app in your organisation? The Atlas AI Insight Platform discovers shadow AI usage including vibe-coded apps connected via OAuth, browser extensions or desktop tools. By Day 30 you have a live register with risk scoring per use case.
- Need a defensible AI policy that covers vibe coding? Our 8-week AI Governance & Risk Assessment includes AI-built-app review criteria and the security checklist your team can adopt as a standard.
AI is powerful. AI with human oversight is the future. AI without it is next year's breach report.